top of page
Search


Tokenisation in AI/LLMs: How It Works and How Pricing Is Calculated
Artificial Intelligence models like OpenAI GPT and Anthropic Claude are widely used in applications such as chatbots, automation tools, content generation, analytics, and more. These models do not process text the way humans read it. They work with tokens . Understanding tokenisation is essential because it directly affects: 💰 Cost ⚡ Performance 📏 Input and output limits 🔹 What is Tokenisation? Tokenisation is the process of breaking text into smaller units called tokens .

Siddhesh Kadam
3 min read


Building Smart Load Balancing Using HAProxy and Custom Health Endpoints
In real-world production setups, checking whether a server is just alive is not enough. A server may respond on port 80, but internally: CPU could be overloaded Memory could be exhausted Requests could be timing out Yet traditional health checks will still mark it as UP . This is where HAProxy httpchk becomes extremely powerful. In this blog, we’ll walk through a practical implementation where HAProxy:👉 Routes traffic based on actual system load , not just availability. �

Siddhesh Kadam
2 min read


Exploring HAProxy Monitoring Techniques
Hands-on HAProxy Monitoring using Stats Socket, Web UI, and HALog HAProxy is one of the most powerful and widely used load balancers in modern DevOps and cloud environments.However, installing HAProxy is only the first step. In real production environments, monitoring HAProxy is extremely important to ensure backend servers are healthy, traffic is balanced correctly, and no errors are happening silently. In this guide, we will explore basic HAProxy monitoring techniques usin

Siddhesh Kadam
3 min read


Filebeat — The Silent Log Shipper
If you manage Linux servers long enough, you eventually hit this moment: Server is slow… users are shouting… and logs are everywhere. /var/log/messages /var/log/secure /var/log/nginx/access.log /var/log/nginx/error.log /var/log/mysql/error.log /var/log/audit/audit.log /app/logs/*.log /docker/containers/*/*.log So what do you do? You SSH into the box and start the ancient ritual: [root@siddhesh ~]# tail -f /var/log/messages [root@siddhesh ~]# tail -f /var/log/nginx/error.log

Siddhesh Kadam
3 min read


From On-Prem MySQL to AWS RDS: A Practical Migration Guide
Introduction When migrating applications to the cloud, databases are often the most critical and sensitive components. A poorly planned database migration can lead to downtime, data loss, or performance issues. In this hands-on guide, we will migrate a MySQL database from a Linux server to Amazon Aurora (MySQL-Compatible) using AWS RDS. This walkthrough is ideal for DevOps engineers, cloud engineers, and anyone learning AWS database migration. What You’ll Learn How to create

Siddhesh Kadam
2 min read

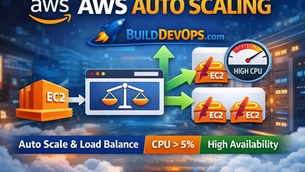
Implementing AWS Auto Scaling Using EC2, ALB & Target Tracking
Introduction In modern cloud environments, auto scaling is critical for high availability, performance, and cost optimization. Instead of running multiple servers all the time, AWS allows you to automatically scale EC2 instances based on load . In this blog, we will configure: Apache Web Server on EC2 Auto Scaling Group (ASG) Launch Template Target Tracking Policy Scale out when CPU > 5% Automatically launch a second Apache instance This setup is ideal for: Web applications

Siddhesh Kadam
3 min read


Monitor AWS EC2 Instance Using CloudWatch and Grafana
Monitoring EC2 instances is a basic but critical task for every DevOps engineer. AWS provides CloudWatch for collecting metrics, and Grafana makes visualisation simple and powerful. In this blog, we will learn how to monitor an AWS EC2 instance using CloudWatch and Grafana , step by step, in a clean and practical way. 🧩 Architecture Overview ✅ Prerequisites Before starting, make sure you have: An AWS account A running EC2 instance IAM user with programmatic access Grafana in

Siddhesh Kadam
2 min read


How to Add Custom Metrics in Prometheus & Grafana
📌 Overview Prometheus Node Exporter provides excellent system-level metrics, but in real-world production environments, we often need custom application metrics — for example: Postfix mail queue size Service status running/failure Application health Queue depth In this blog, we will implement a custom Node Exporter metric to monitor postfix mail queue and visualise it in Grafana , using the textfile collector, the recommended and production-safe approach. 🧠 Architecture

Siddhesh Kadam
2 min read


What Really Happens When You Shutdown a Linux Server ?
Introduction A Linux shutdown is more than just turning off a machine — it is a controlled process that protects running services, active users, and critical data. Understanding what happens during shutdown helps administrators troubleshoot delays, prevent corruption, and manage systems more confidently. [root@siddhesh ~]# shutdown -h now But very few actually know what happens after this command is executed . A shutdown is not just turning off the power.It is a well-orches

Siddhesh Kadam
3 min read


Building a CI/CD Pipeline with AWS CodeCommit & CodePipeline to Deploy a Static Website on S3
AWS CodePipeline provides a native AWS continuous deployment pipeline to manage web application deployments from the source code repository to the deployment of our web application. In this blog, we will walk through setting up AWS CodePipeline to continuously deploy our web application to S3 . We will walk through the prerequisites to set up our pipeline by setting up our source code repository with AWS CodeCommit and creating an S3 bucket to host static web application

Siddhesh Kadam
2 min read


From Install to Injection: Hands-on SQLMap Tutorial on Linux
Disclaimer : This blog is strictly for educational and authorized security testing only. Always take written permission before testing any application. Unauthorized testing is illegal. Introduction SQL Injection is still one of the most common and dangerous web vulnerabilities. Even today, many internal tools, admin panels, and legacy applications are exposed due to weak input validation. sqlmap is an open-source penetration testing tool that automates the process of detect

Siddhesh Kadam
3 min read


Advanced Intrusion Detection Environment (AIDE) on RHEL / Rocky / CentOS
System integrity is one of the most overlooked areas in Linux security. Firewalls, SELinux, and antivirus tools are common, but they do not tell you if critical system files were modified silently . This is where AIDE (Advanced Intrusion Detection Environment) fits perfectly. In this blog, I’ll walk through what AIDE is, how it works, how to configure it properly , and how to interpret its output on RHEL, Rocky Linux, and CentOS . All commands shown below were executed manu

Siddhesh Kadam
3 min read
bottom of page






